Global cyber attacks — like WannaCry and Petya — affected thousands of targets and networks around the world. Even if you escaped these, attacks targeting an industry, company or country can cause as much damage, whether the goal is to disrupt operations, gain attention or ransom data.
We’re beginning to see companies not just think about cybersecurity from the perspective of defense in depth, but also starting to adopt capabilities that allow them to address cyber risk across an attack continuum. They’re doing this by focusing in on the five functions addressed in the NIST cybersecurity framework:
- Identifying what they have and the associated risks.
- Placing protection mechanisms in place to protect what they have.
- Detecting when threats bypass those protection mechanisms.
- Implementing capabilities to respond to incidents more quickly.
- Developing a system to support rapid recovery.
Right now I’d say manufacturers are getting better at basic cyber hygiene.That approach starts with not just understanding what is connected on your plant floor, but its attack surface. In other words, what are those assets’ vulnerabilities? Then use that knowledge to address the known vulnerabilities by patching them. To help minimize your risk, consider a security program focused on four key areas:
- Maintain an asset inventory with an emphasis on understanding the attack surface or vulnerability.
- Vulnerability, patch and configuration management. Have programs in place to address known vulnerabilities, patch regularly and have mature processes around how configuration changes are made and tracked.
- Employ backup and recovery mechanisms for all critical assets to help ensure you have the ability to quickly pull from a known good backup.
- Complete regular risk assessments to measure risk and manage it. Use the assessments to show your organization the level of risk they are exposed to and the resources (time, money, people) needed to mitigate it.
Successfully implementing these tenets of basic cyber hygiene are the first steps in building an effective cyber security program for your organization and improving your ability to defend against future cyber attacks. We’re beginning to see companies not just think about cyber security from the perspective of defense in depth, but also starting to adopt capabilities that allow them to address cyber risk across an attack continuum.
A key tenet of basic cyber hygiene is the ability to address known vulnerabilities. But in some instances a vendor might no longer support a critical asset. Consider the following questions when evaluating the overall risk of maintaining obsolete hardware or software:
- What is the impact of someone exploiting this vulnerability?
- Is there a way to address this vulnerability through the application of an alternative mitigating control?
- If not, can I justify migrating to a supported platform/solution/product set for this application?
The answers to these questions become the basis for your discussions around mitigation and migration. You can begin budgeting funds to move from basic cyber hygiene to an industrial cyber program that allows you to continually evaluate risk and match funding and resources to keep that risk at a tolerable level.
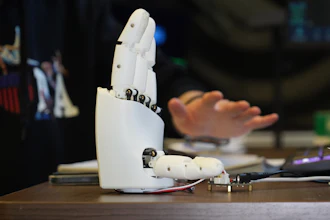
For all the benefits that smart manufacturing can offer, it also requires a more comprehensive approach to security. Seamless connectivity and smart devices are the catalysts to smart manufacturing — they but can also be a conduit for security threats.
To see this blog from Rockwell Automation in its original form, click here.