The efficiency, power, and flexibility of interconnected, remotely accessible industrial IIoT systems championed in the Industry 4.0 era does have one major drawback.
When it comes to critical manufacturing, infrastructure, and transportation hardware or software - industrial cybercrime has far-reaching consequences beyond the purely financial. The more functionality exposed to public or private networks, the more exposure and points of access there are for malicious actors. In the current climate of increased industrial cyber attack risk, how do you effectively plan?
With the global cost of cybercrime in the trillions, cyberattacks cost U.S. businesses an average of $1.7M per breach, focusing on the direct financial cost. In addition to being a major financial and business-continuity disruption, a cyberattack can erode confidence and public trust - both of which are critical factors in today’s business landscape.
Reputation loss among vendors, peers or clients can significantly affect future business. There can also be other ancillary effects that derive from a remote takeover or unplanned shutdown due to an attack, such as environmental or logistical issues that could take months to resolve. In addition, insurance premiums increase and investors may lose confidence.
Through careful planning and implementation using modern cyber-physical protection systems, companies can leverage the benefits of IIoT while maintaining the defense of their networks, devices, and data from intrusion. Cyber threat detection is important, but accompanying physical response systems provide better protection by quickly and automatically taking mitigating action against cyberattacks.
Defense in Depth
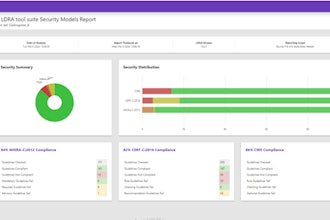
Defense-in-Depth’ (DID) protection is both broad in scope and layered (‘in-depth’), as recommended by the international standard IEC 62443. DID focuses on creating multiple layers of security, so in case one fails, others remain to protect a facility and its assets. It exists at three levels:
- Plant Security is the implementation of methods to prevent unauthorized persons from gaining physical access to the plant floor, critical components and determining who and what are allowed in and out. This refers to personnel, devices, and information. Plant security also addresses the need for organizational policies and procedures to maintain resilient cyber protection.
- Network Security focuses on measures to secure Operational Technology (OT) networks and machines, including verified and trusted devices that are supposed to transmit data.
- System Integrity is designing systems and machines with integrated cybersecurity protections.
Only by implementing both all-round and in-depth protection can a company truly secure industrial operations. Fortunately, there are tools and best practices to achieve each of these in mounting a strong, layered defense against cyberattacks.
Focusing on System Integrity
System Integrity is a crucial aspect of these defensive layers that may have not been fully implemented in some industrial settings. The focus on the protection of automation systems and control components typically includes:
- Access Control
- Access Protection and Authentication
- User Management
- Communication Integrity
- Know-how (IP) Protection
- Copy and Execution Protection
System integrity protections act as a last line of defense, designed into the hardware itself, even when the physical or network security has been breached. The PLC system can be protected at several levels, extending all the way to a complete lockdown if necessary.
Efficient user administration should be implemented for access control to network components that authenticates users and authorizes accesses and use. Digital checksums, when accessing controllers, can protect communication against unauthorized manipulation. Binding individual program blocks to the PLC’s serial number or memory card prevents the duplication of projects and makes it possible to detect manipulation attempts.
The challenges in industrial cybersecurity are unique because the stakes are high. There can be risk for the plant, the business, and even people's lives. Mitigating the risk of cyberattacks cannot be an afterthought or a cursory process. To implement a layered defense that encompasses software, hardware, and business processes, planning must include stakeholders from the physical site security team, the IT department, machine designers and plant decision-makers.
Efficient, networked industry is the only way to stay competitive, but that doesn’t mean giving up operational peace of mind. With Defense-In-Depth, strong processes are backed up by software and automated responses that are baked into the hardware. These solutions are configured and ready to take action via a careful design and deployment of layered cybersecurity safeguards.
Luis Narvaez is the U.S. Product Marketing Manager for SIMATIC PLCs and Industrial Security at Siemens Industry, Inc.